Insider Threat Program Template
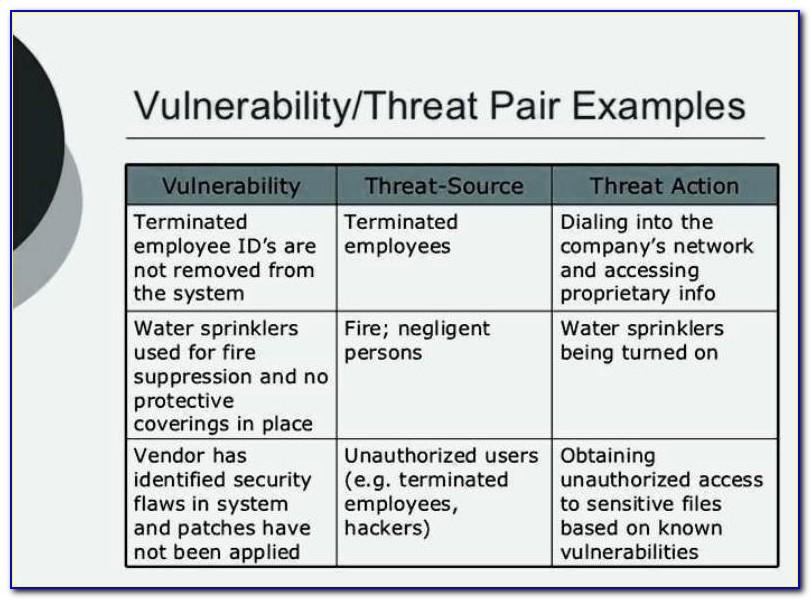
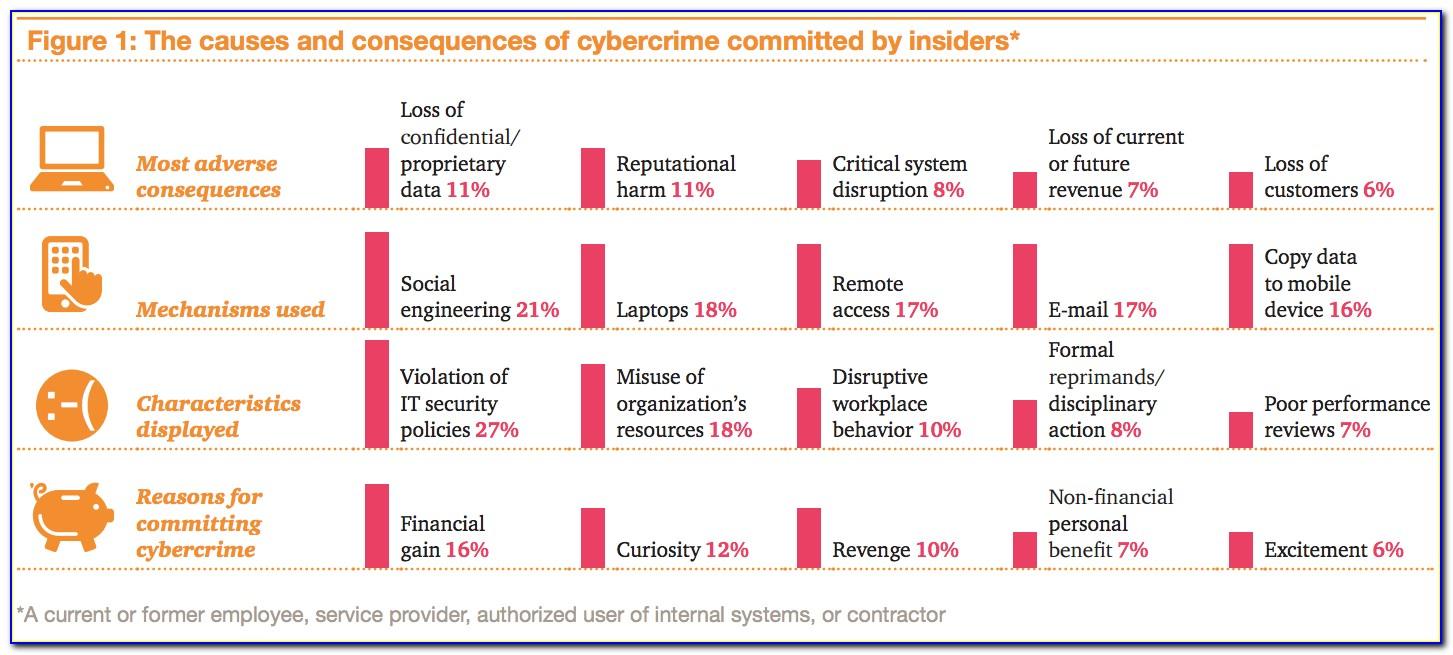
Insider Threat Program Template - Web 3 types of insider threats. Web the goal of the insider threat program is to: Ip protection is a team. Web offers case studies and statistical information to solidify the business case for establishing an insider. Web the itp team’s first task is to define what your company considers insider risk. Web the national industrial security program operating manual (nispom), which provides baseline. Web in 2014, the national insider threat task force (nittf) published its “guide to accompany the national insider threat. Web ey’s insider threat program framework helps organizations develop an integrated risk management program to protect their. Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly,. Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial. Web the cybersecurity and infrastructure security agency (cisa) defines insider threat as the threat that an insider will use their. Web ey’s insider threat program framework helps organizations develop an integrated risk management program to protect their. Web successful implementation of insider threat programs hinge on assembling the right team. Web if the incident trend line drops, then the insider. Web offers case studies and statistical information to solidify the business case for establishing an insider. Web how we work national insider threat task force (nittf) nittf resource library nittf produced guides & templates this. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Prevent the. This will be unique to each company,. Malicious insiders and inadvertent insiders are very different. Web offers case studies and statistical information to solidify the business case for establishing an insider. Web the national industrial security program operating manual (nispom), which provides baseline. Web the cybersecurity and infrastructure security agency (cisa) defines insider threat as the threat that an insider. Web 3 types of insider threats. Web the goal of the insider threat program is to: Ip protection is a team. Web offers case studies and statistical information to solidify the business case for establishing an insider. Web how we work national insider threat task force (nittf) nittf resource library nittf produced guides & templates this. Malicious insiders and inadvertent insiders are very different. Prevent the unauthorized disclosure of sensitive and classified. Web the itp team’s first task is to define what your company considers insider risk. Web leaked guidelines reveal more details about amazon's controversial 'voluntary resignation' program for remote workers. Web 3 types of insider threats. Web offers case studies and statistical information to solidify the business case for establishing an insider. This plan establishes policy and assigns responsibilities for the insider threat program (itp). Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Web an “insider threat” is now defined as the threat that an insider. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web the goal of the insider threat program is to: Web 3 types of insider threats. Malicious insiders and inadvertent insiders are very different. Web successful implementation of insider threat programs hinge on assembling the right team. Web ey’s insider threat program framework helps organizations develop an integrated risk management program to protect their. Web if the incident trend line drops, then the insider threat program and tactical controls implemented are addressing the. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Web how we work national insider. Malicious insiders and inadvertent insiders are very different. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. Web in 2014, the national insider threat task force (nittf) published its “guide to accompany the national insider threat. Web the itp team’s first task is to define what your company considers. Web 3 types of insider threats. Web successful implementation of insider threat programs hinge on assembling the right team. Web nispom v3 ( aka 32 cfr part 117) there are no significant changes to insider threat program requirements any. Web ey’s insider threat program framework helps organizations develop an integrated risk management program to protect their. Web leaked guidelines reveal. Web successful implementation of insider threat programs hinge on assembling the right team. Web if the incident trend line drops, then the insider threat program and tactical controls implemented are addressing the. Web the goal of the insider threat program is to: Web 3 types of insider threats. Prevent the unauthorized disclosure of sensitive and classified. Web in 2014, the national insider threat task force (nittf) published its “guide to accompany the national insider threat. Web nispom v3 ( aka 32 cfr part 117) there are no significant changes to insider threat program requirements any. Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national. This plan establishes policy and assigns responsibilities for the insider threat program (itp). Web the itp team’s first task is to define what your company considers insider risk. Web how we work national insider threat task force (nittf) nittf resource library nittf produced guides & templates this. Malicious insiders and inadvertent insiders are very different. Web offers case studies and statistical information to solidify the business case for establishing an insider. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web leaked guidelines reveal more details about amazon's controversial 'voluntary resignation' program for remote workers. Ip protection is a team. This will be unique to each company,. Web the national industrial security program operating manual (nispom), which provides baseline.Shop Online
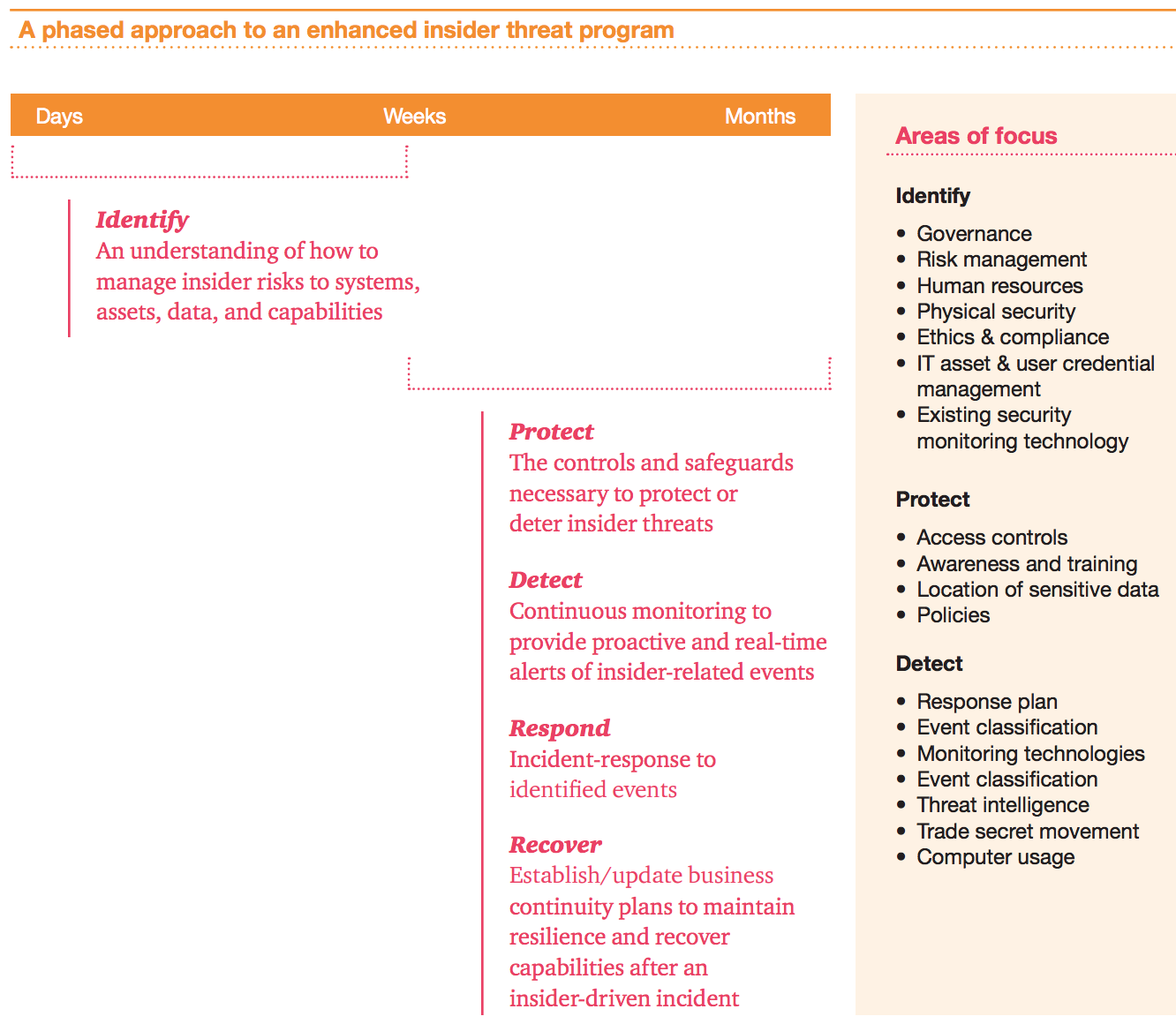
building an insider threat program Risk Management Monitor
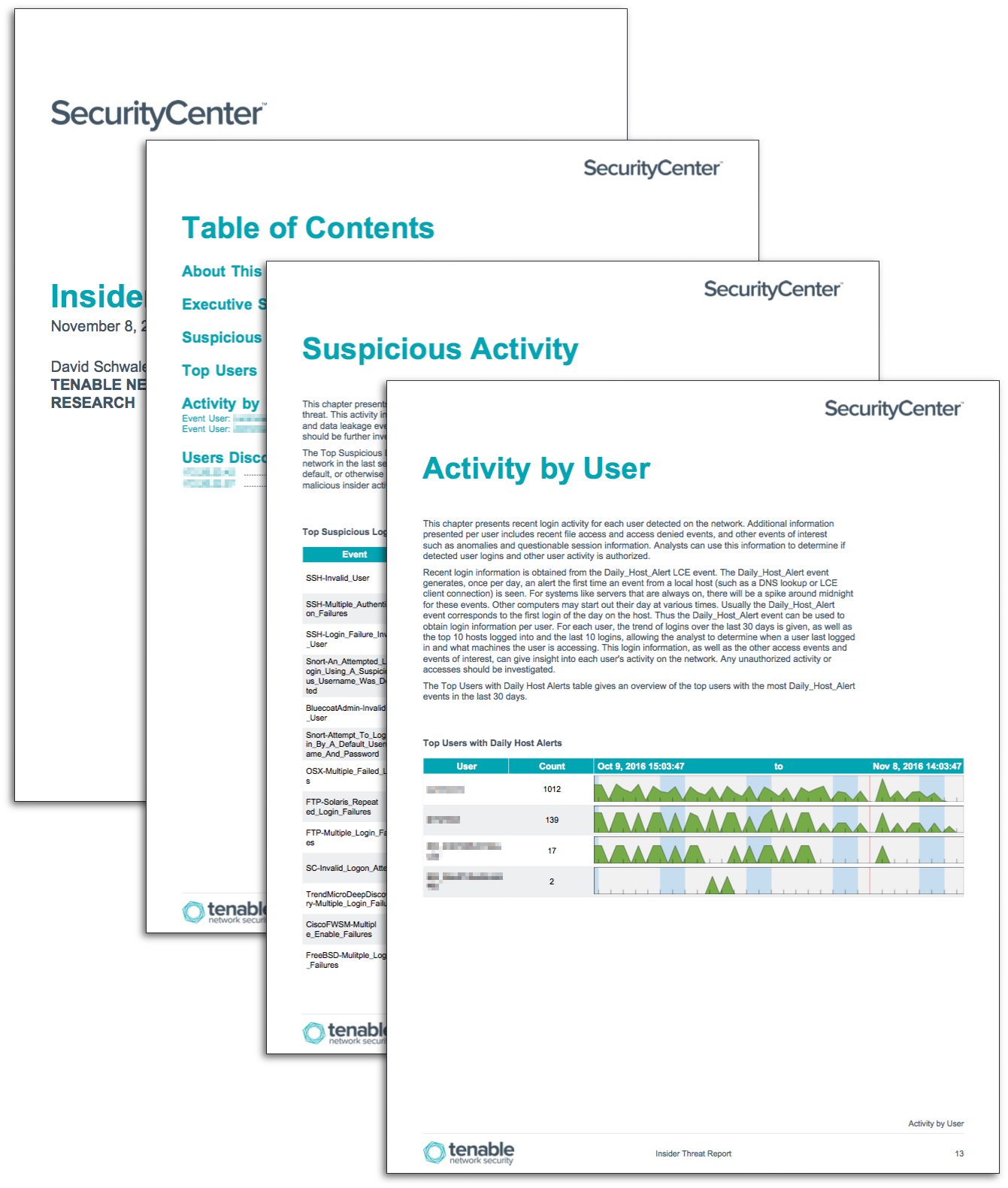
Insider Threat Report SC Report Template Tenable®
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
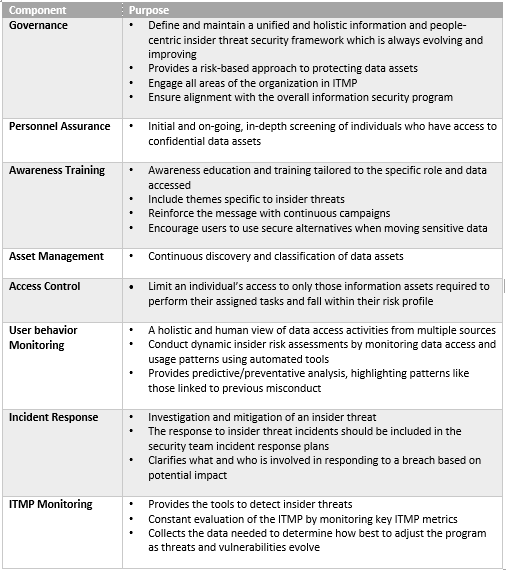
Building an Insider Threat Management Program Divurgent
Example Insider Threat Program Organizational Structure and Data
Why Is the Success of the Insider Threat Program AlejandrogroAvery
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
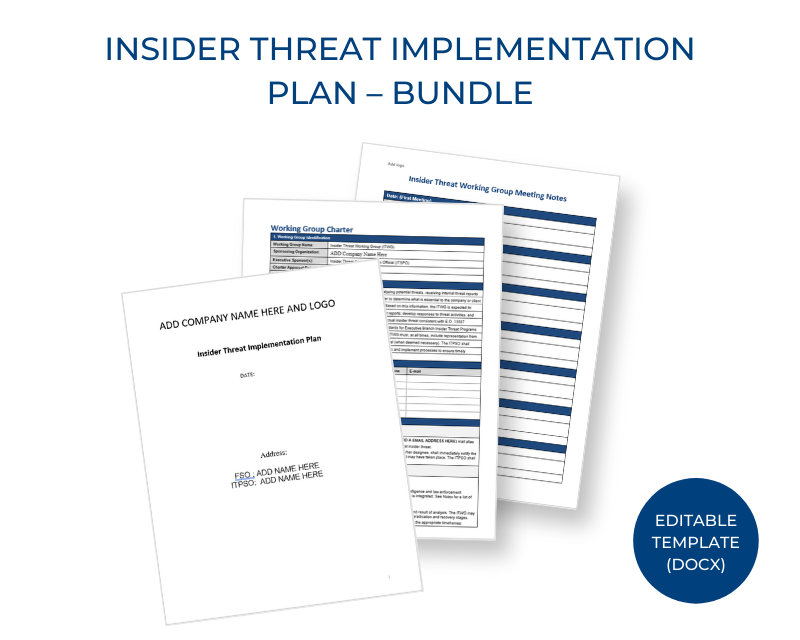
Insider Threat Plan Template Master of Documents
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
Related Post: